Due to a fault, the Google Home smart speaker could be remotely controlled. Unfortunately, it also turned into a snooping device by installing a backdoor account with access to the microphone feed.
Last year, researcher Matt Kunze found the problem and was awarded $107,500 for appropriately alerting Google to it. Earlier this week, the researcher shared technical information on the discovery and an attack scenario to demonstrate how the issue may be exploited.
The researcher found that new accounts created using the Google Home app may remotely control it via the cloud API while exploring with his own Google Home tiny speaker.
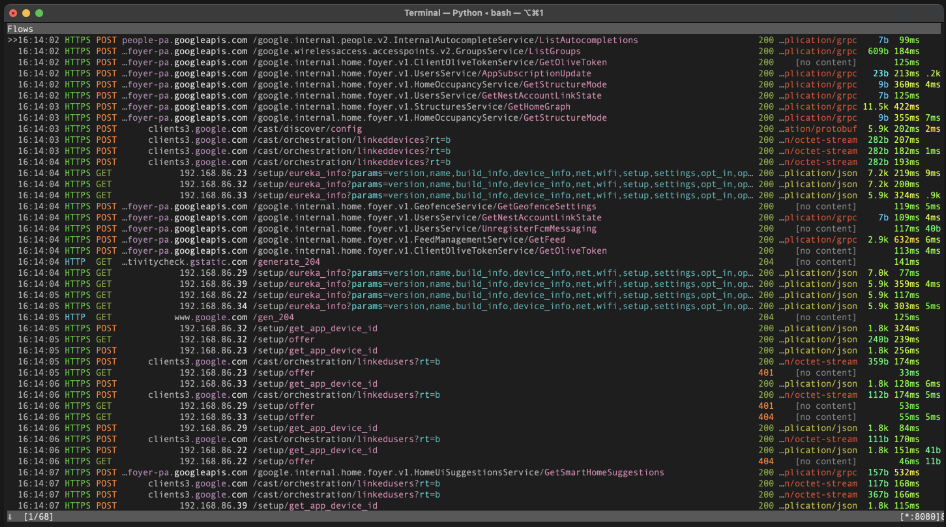
The researcher discovered Google Home’s local HTTP API port using a Nmap scan. So he put up a proxy to collect the data over HTTPS in an effort to intercept the user authorization token.
The researcher noticed that adding a new user to the target device involves two steps and calls for the local API’s “cloud ID,” “cloud certificate,” and device name. Then, they might submit a link request to the Google server using this information.
Researcher posted three proofs of concepts
The analyst automated the exfiltration of the local device data and replicated the linking request by implementing the link procedure in a Python script to add a malicious user to a target Google Home device.
The researcher posted three proofs of concepts (PoCs) for the behaviors mentioned above on GitHub. However, the most recent firmware upgrade should prevent them from functioning on Google Home devices.

The PoCs go beyond creating a rogue user by allowing microphone eavesdropping. Also, arbitrary HTTP requests on the victim’s network, and arbitrary file reading/writing on the target device.
The Google Home speaker may perform operations like activating smart switches, making online purchases, remotely unlocking doors and automobiles, or covertly brute-forcing the user’s PIN for smart locks when a rogue account is connected to the target device.
Google Home Speakers performs various operations
What’s more concerning is that the researcher discovered a way to misuse the “call [phone number]” command by incorporating it into a malicious code that activated the microphone at a predetermined time, called the attacker’s number, and sent live microphone feed. The only sign of anything happening during the conversation is when the device’s LED turns blue.
The victim could believe the gadget is upgrading its firmware if they detect it. The typical LED that pulses when the microphone is active does not do so when a call is in progress.
Finally, it can also play music, rename, reboot, erase any saved Wi-Fi networks. Moreover, force new Bluetooth or Wi-Fi pairings, and perform other operations on the hacked smart speaker.
In March 2021, Kunze supplied more information and proof of concepts after discovering the problems in January 2021. Google completed all issues in April 2021.
The update adds a brand-new invite-based method to manage account connections that prevents any tries not already placed on Home. The Local Home SDK was launched in 2020. The scheduled routines were added in 2018, and Google Home was deployed in 2016. Therefore an attacker who discovered the flaw before April 2021 would have had plenty of time to exploit it.











