
Image Credits: MacRumors
Has your Mac been acting odd of late? Does it arbitrarily open pop-ups and lead you to website pages you would rather not see? Or on the other hand, has it begun being unreasonably lazy?
We know how unpleasant the odd way of behaving from your gadget can be. However, here’s the uplifting news — this typically isn’t something too interesting to even consider settling. Odds are your OS is confronting a minor error that will just take a framework reboot to fix. In any case, on the off chance that this doesn’t work, then, at that point, be cautioned: your Mac could have been tainted with malware.
Moves toward Remove Malware From Your Mac
Stage 1: Disconnect your gadget from the web
The main thing you really want to do is detach your Mac from the web to stop any correspondence between it and the malware server. You could have to remain disconnected as long as the gadget stays contaminated. This implies the harm done by the infection can be controlled without its gamble spreading considerably further.
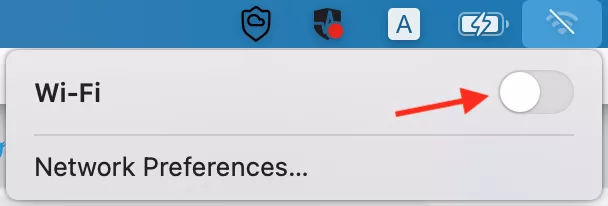
Switch off the Wi-Fi. Separate your Mac from the Internet by turning off the Wi-Fi switch.
The evacuation cycle could expect you to download some outsider instruments. If so, you should download the product right away, then disengage after you’re finished.
Stage 2: Enable protected mode
Protected Mode is an underlying capacity that makes your Mac run on a negligible burden — sending off just the important programming for the boot cycle. While sending off in Safe Mode, the OS likewise performs looks at expected to impede any extra programming attempting to run. Assuming that the infection on your machine is set to stack naturally on boot, it will not have the option to begin. This implies it will be simpler for you to erase malware from your macintosh while it’s not running.
To enter experimental mode:
- Begin your Mac and quickly press and hold the Shift key;
- Discharge the key when the login window springs up.
- Ensure you don’t sign into delicate records or uncover any saved passwords. The malware could follow your keystrokes and set you in a more weak position on the off chance that this occurs. You could likewise be cautious with composing or showing any by and by recognizable data on the screen for a similar explanation.
- Boot in the Safe Mode
- That is the thing you see when you boot in the Safe Mode
Stage 3: Examine the movement screen for strange action
As we previously examined, specific sorts of malware could put an inordinate burden on your CPU and dial it back. The Activity Monitor can be a splendid instrument to check for such issues and fix them.
To open your Activity Monitor:
Press Cmd + Space
Begin composing ‘Action Monitor’ in the pursuit field
Click on Activity Monitor
When you have it before you, search for any dubious applications in the Processes region. You may likewise glance through the CPU tab to check for heavier applications. Assuming you truly do find any dubious applications or even an update, close it through the screen, then, at that point, erase it from the Finder menu.
Stage 4: Use an enemy of malware programming
Hostile to Malware programming frequently works effectively consequently following and eliminating PC infections. The more grounded ones even safeguard your PC from ransomware and different dangers. To filter Mac for malware and eliminate it:
- Download and introduce Clario, make a record
- Introduce Clario
- Go to Apple menu > System Preferences > Security and Privacy and permit Clario Full circle access
- Permit Full plate access
- Press Quick sweep
- Check your Mac
- Eliminate identified dangers
Stage 5: Double-actually take a look at your program expansions
Most malware and adware enter your framework through your web program and frequently introduce an expansion of some kind. They might try and screw with your program settings to make it difficult to eliminate the augmentation in any case, albeit this is very uncommon. Generally speaking, erasing the program augmentation finishes the work.
In the event that you’re utilizing Google Chrome, you can follow these moves toward actually looking at the introduced expansions and eliminate some of the vital:
- Select the three vertical dabs on the upper right of your program screen
- Select Settings starting from the drop menu that shows up
- Click Extensions to see all
- Deal with your Chrome expansions
- Access your Chrome expansions to erase the dubious ones
- Erase dubious expansions
- Reboot the framework for the impact to happen
- On the off chance that you’re on an alternate program, the means will be comparative.
Stage 6: Check for malware in macintosh login things
Login things incorporate the applications that start each time you send off your OS. Now and again, these applications are important to run the OS, and at different times, they are futile and can house various kinds of infections. You really want to check your login things and handicap the ones that might be going about as a cover for malware.
This is the way to do this:
- Click on the Apple logo on the menu bar
- Click on System Preferences and afterward Users and Groups
- Click on the lock in the lower-left corner
- Open Login Items
Stage 7: Remove every dubious application
At last, you should go through all the introduced applications to check in the event that there are some you won’t ever utilize. When you have them shortlisted, lead a legitimate examination on each application to figure out the utilization. For most cases, a basic Google search will uncover if an application is helpful or just a cover for malware.











