Microsoft is one of the most forward-looking companies in the entire technology industry and with its big-name and huge resources, the company is bringing the future to its consumers very actively. From Windows 11 to Microsoft’s cloud computing systems, the company has been actively working on projects that innovate and make tomorrow better than yesterday.
But unfortunately, Microsoft, with its giant technology company reputation, has been in the dump lately. According to recent resources, the Windows-maker has yet again been targeted by another cyber attack, and this time it is Microsoft’s Azure cloud computing service that has left sensitive data of thousands of customers vulnerable and susceptible to cyberattacks.
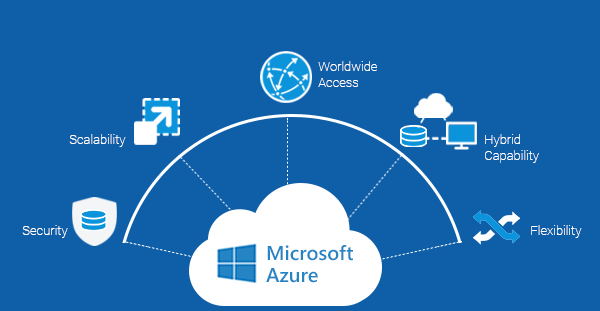
Microsoft Azure is a flagship cloud computing service whose customers include some big-name including Coca-Cola, Exxon-Mobil, and several Fortune 500 companies. Soon after the threat was discovered, the Windows-maker intimated its clients and warned them of the flaw in their flagship database service called “Cosmos DB” as mentioned in a report by Engadget.
The report further claims that Wiz named this vulnerability as “Chaos DB” and it allowed anyone to get unrestricted access to accounts and databases of thousands of Microsoft Azure customers. As you must have noticed by now, it is a blunder but I guess, Microsoft is in the habit of making the headlines with cyber-attacks and potential vulnerabilities.
Microsoft explained the vulnerability in their Cosmos DB feature called Jupyter Notebook that allowed customers to visualize their data. However, the blunder happened with a series of misconfigurations in the Jupyter Notebook that ultimately created a loophole allowing any random user to view, download, delete and manipulate data from the massive collection of commercial databases. All in all, the entire Microsoft Azure user database was vulnerable to anyone changing any aspect of it.
Furthermore, the company has issued a statement saying that the vulnerability could have been active for days, weeks, months, or possibly years, and the team is now advising all Azure customers to regenerate their access keys as a precautionary measure.
The good news is that there was no exploitation of this vulnerability before it was found and other than Wiz, no party had access to the primary read-write key of the Microsoft Azure database, as mentioned in a report by Engadget.
I hope you are aware of Microsoft’s recent SolarWinds attack that took the industry by storm. The question here is, if Microsoft is unable to keep its own services safe and out of attack, how can the government of the United States expect Microsoft to assist in local, state, and federal security? I think we will have to wait and see what happens.










