Pegasus is making headlines once again. In India, the last time we heard about this was in 2019, when certain WhatsApp users particularly journalists and activists, received alerts from WhatsApp claiming that they were affected by Pegasus and their smartphones were vulnerable. It appears to be used so regularly by various countries throughout the world that there are instances of a phone being hacked using it nearly every few months.

Boonchai Wedmakawand via Getty Images
A number of major news outlets, including the Guardian and the Washington Post, revealed details of what they labeled global monitoring operations involving the highly advance Pegasus Software on Sunday. According to reports, the surveillance is targeted at senior journalists, including over 40 in India, activists, and other notable personalities. According to the reports, Pegasus malicious software is being used to spy on individuals across 10 nations, including India.
What really is Pegasus software?
Pegasus is a piece of software and labeled as spyware that has been created by NSO Group, an Israeli firm that is highly specialized in developing cyberweapons. The malware is engineered beyond your consent to access your device, collect and communicate with your personal data to anyone who uses the software to spy on you. It originally made headlines in 2016, when an Arab activist became suspicious after receiving a malicious message. Pegasus was considered to be targeting iPhone users. A few days after its finding, Apple issued an updated version of iOS that allegedly fixed the security vulnerability that Pegasus was exploiting to attack phones.
Pegasus, however, was later discovered to be correspondingly capable of infecting Android devices a year later by cybersecurity experts, after which a series of patches were rolled out. Facebook later in 2019 filed a lawsuit against the NSO Group for developing Pegasus. The spyware was thoroughly investigated by Facebook security professionals across their platforms, and they discovered that the malware had been used to infect numerous journalists and activists in India using its instant messaging app WhatsApp.
So how does the Pegasus Spyware work?
Pegasus’ ability to break into phones is one of the reasons why it is widely used. The phone hacking is literally unnoticeable, and the user has no idea their device has been infected with any sort of malware or spyware in this case. Using a phishing link, a hacker commonly tries to penetrate the device of a target with Pegasus, mainly through a text message or voice calls, which seems harmless and unobjectionable.
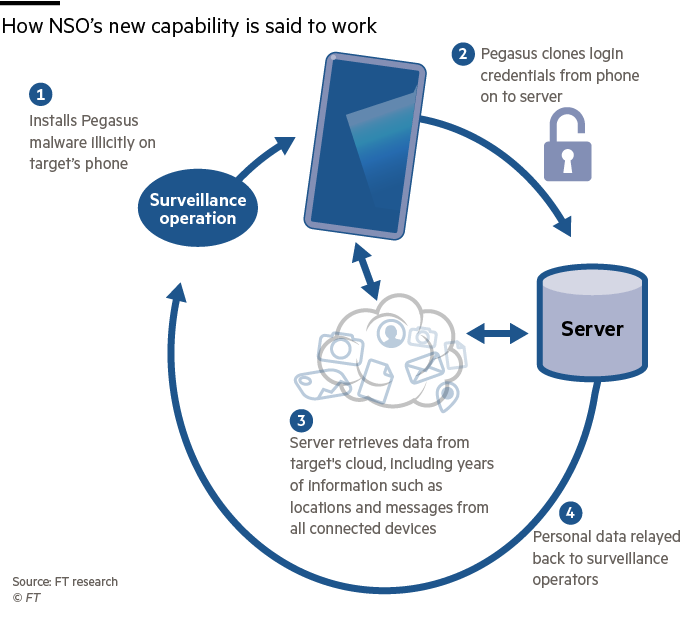
Clicking on the phishing link or receiving the voice call would trigger the installation of Pegasus on the victim’s device and establish a connection with a hacker’s controlling machine, which may be thousands of kilometers away. Once the spyware is deployed, it will automatically delete the call log or the chat history entry so the target would not be aware of that call or text message.
The hacker can then connect with the Pegasus spyware through the remote control center and employ the spyware on what information to report back to the hacker’s server. Some researchers also highlighted that the spyware can also collect passwords, contact lists, calendar events, text messages, and live voice calls from popular mobile messaging apps. Furthermore, it can also intercept encrypted audio streams and encrypted messages.
Since NSO created Pegasus for targeted surveillance on handpicked victims, not just everyone, this highly advanced piece of code can “self-destructs” itself if it can’t establish a connection with the hacker’s control center for more than 60 days or when it “detects” that it’s been planted on a device with the inappropriate SIM card.










