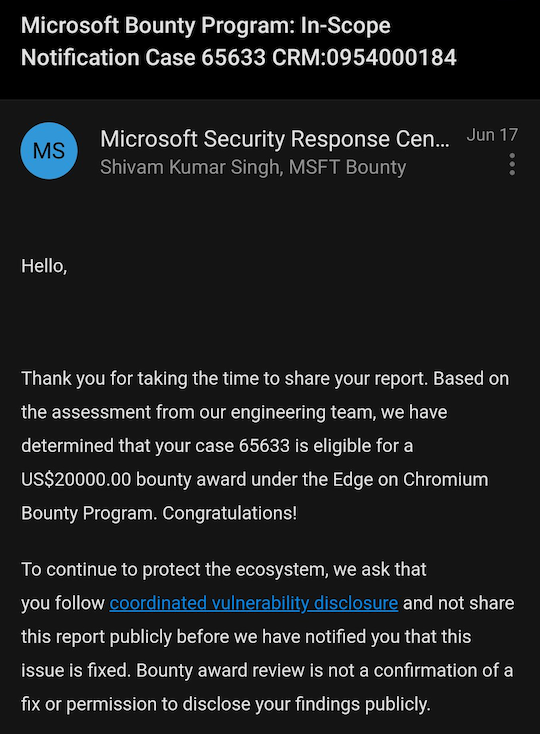
For identifying vulnerabilities in the Microsoft Edge browser, two Indians, Vansh Devgan from Uttar Pradesh and Shivam Kumar Singh from Jharkhand, along with their Russian friend Ignacio Laurence have won a huge bounty reward. They discovered two “vulnerable code” that involves uXSS (Universal Cross-Site Scripting) in Microsoft’s Translator and which comes pre-installed in the Edge browser. For identifying the security flaws and notifying them to the company, Microsoft has rewarded the duo with $20,000 (to approx. 15 lakh).
Last week, Microsoft patched two bugs in its Chromium-based Edge browser, one of which may allow an attacker to bypass security and remotely inject and execute arbitrary code on any website simply by sending a message. CVE-2021-34506 is a major security flaw with a CVSS rating of 5.4. It has a low level of complexity, and an attacker could carry it out without requiring any specific set of permissions, according to Microsoft, which issued the patches on Thursday. However, an exploit would need user interaction.
Whenever the language translation feature in Microsoft Edge is used, the security vulnerability gets activated. If a user browses any website using Edge Chromium, chooses the language-translation tool, an arbitrary code could be triggered to execute any action, giving access to the attacker. As a result, executing arbitrary code was relatively simple, as it only required enabling the auto-translate in Microsoft Edge. However, Microsft has released the patches as mention earlier, and users are urged to update to version 91.0.864.59 of the browser.
These bounty hunters have shown that the attack might be triggered simply by adding a comment to a YouTube vídeo that is in a language different than English and an XSS payload as a proof-of-concept (POC) exploit.
Similarly, a friend request from a Facebook account containing other language content with the XSS payload was detected to execute the code as soon as the recipient viewed out the user’s profile. Vansh Devgan further explains, “We created a profile on Facebook with name in a different language and XSS payload and sent a friend request to the victim (he is using Microsoft edge) as soon as he checks our profile he got hacked (SCC popup because of auto-translation).”

Talking about the two Indians who discovered these vulnerabilities, Shivam is a part-time bug bounty hunter, while Vansh has completed his third year in B.Tech Computer Science from Lovely Professional University and is running CyberXplore Private Limited along with his friend Shivam Kumar Singh.





